一. 如果您想使用数字4624(这通常是Windows事件查看器中的一个事件ID,表示一个帐户已成功登录)来筛选系统的用户登录成功情况,您通常会在Windows的事件查看器(Event Viewer)中进行此操作。
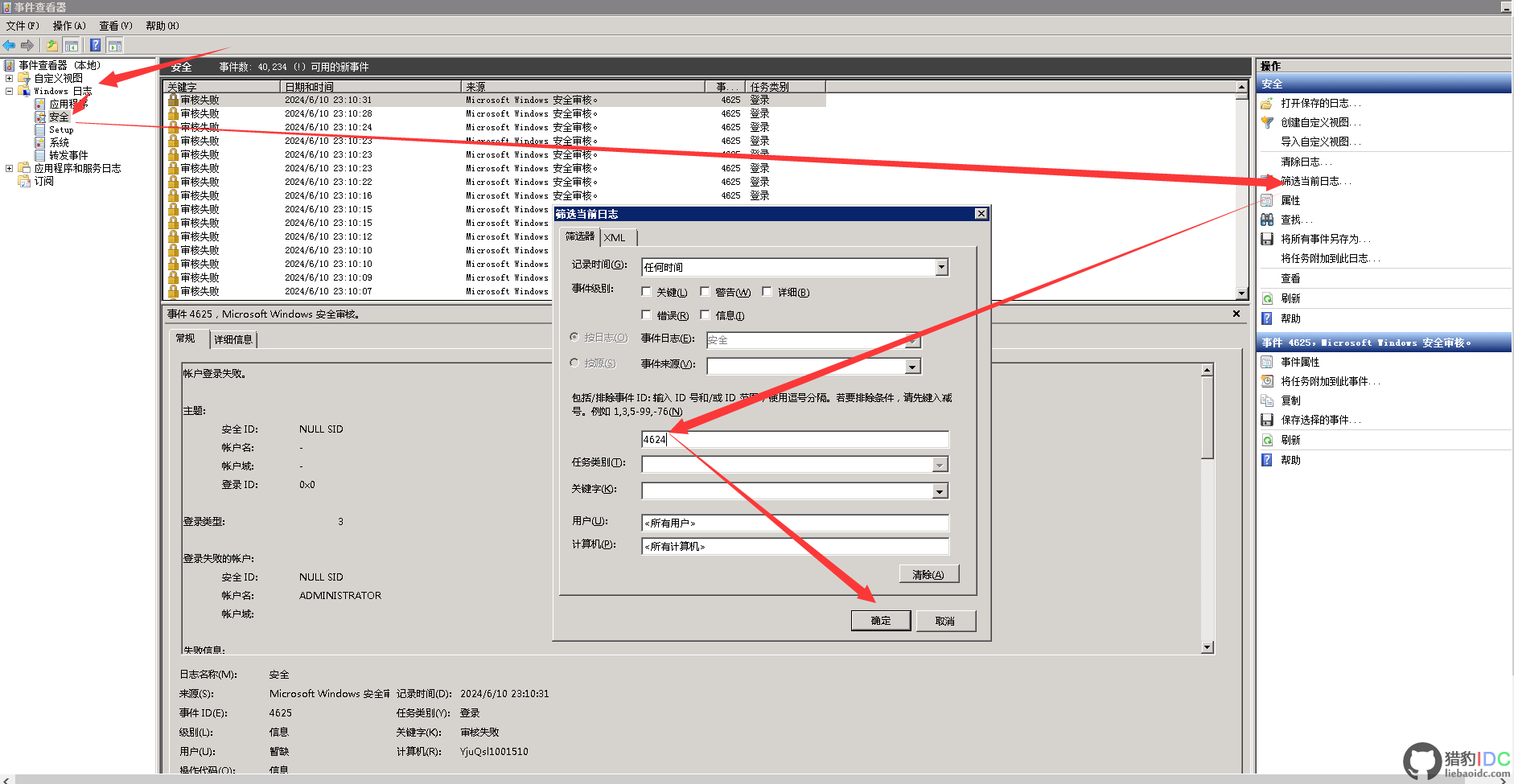
以下是如何在Windows事件查看器中筛选4624事件ID的步骤:
-
打开事件查看器:
- 点击桌面做下角 "开始"-->"运行" , 或 按下Win + R键打开“运行”对话框。
- 输入eventvwr.msc并按下Enter键。
-
导航到Windows日志:
- 在事件查看器的左侧窗格中,展开“Windows日志”。
- 点击“安全”。
-
筛选事件:
- 在右侧窗格的顶部,您应该看到一个“筛选当前日志...”的链接。点击它。
- 在弹出的对话框中,转到“事件ID”部分。
- 在“事件ID”框中输入4624。
- 点击“确定”。
现在,您应该只看到与事件ID 4624(即成功登录事件)相关的事件。
-
查看和分析事件:
- 您可以查看每个事件的详细信息,包括登录的用户、登录类型、登录来源等。
二. 在Windows系统中,安全事件ID是用于跟踪和记录系统安全相关活动的重要标识符。以下是Windows安全事件ID的汇总,按照不同的类别进行分类和解释:
用户帐户相关事件
- 4624:成功登录事件,表示用户成功登录系统。
- 4625:登录失败事件,表示用户尝试但未能成功登录系统。
- 4720:创建用户事件,表示新用户帐户已创建。
- 4722:启用用户帐户事件,表示禁用的用户帐户已被启用。
- 4723:更改用户密码事件,表示用户密码已更改。
- 4738:设置用户密码事件,表示用户密码已更改或重置(注意与4723事件类似,但可能有不同触发条件)。
- 4740:用户帐户已被锁定,表示用户帐户因多次登录失败等原因被锁定。
用户组相关事件
- 4731:已创建启用安全性的本地组。
- 4732:已将成员添加到启用安全性的本地组。
- 4733:成员已从启用安全性的本地组中删除。
- 4734:已删除已启用安全性的本地组。
- 4735:已启用安全性的本地组已更改。
- 4737:启用安全性的全局组已更改。
计算机帐户相关事件
- 4741:已创建计算机帐户。
- 4742:计算机帐户已更改。
- 4743:计算机帐户已删除。
安全组相关事件
- 4724:创建安全组事件,表示新安全组已创建。
- 4754:已创建启用安全性的通用组。
- 4755:启用安全性的通用组已更改。
安全性设置相关事件
- 4739:域策略已更改,表示域的安全策略已发生更改。
- 4764:组类型已更改,表示用户组(如本地组、全局组、通用组)的类型已发生更改。
其他安全事件
- 1100:事件记录服务已关闭。
- 1101:审计事件已被运输中断。
- 1102:审核日志已清除。
- 1104:安全日志现已满。
- 1105:事件日志自动备份。
- 1108:事件日志记录服务遇到错误。
系统相关安全事件
- 4608:Windows正在启动。
- 4609:Windows正在关闭。
- 4610:本地安全机构已加载身份验证包。
- 4611:已向本地安全机构注册了受信任的登录进程。
- 4612:为审计消息排队分配的内部资源已经用尽,导致一些审计丢失。
请注意,这些事件ID可能因Windows版本和配置的不同而有所差异。在实际使用中,建议参考具体的Windows文档或系统日志以获取最准确的信息。
 相关文章
相关文章  售前咨询
售前咨询